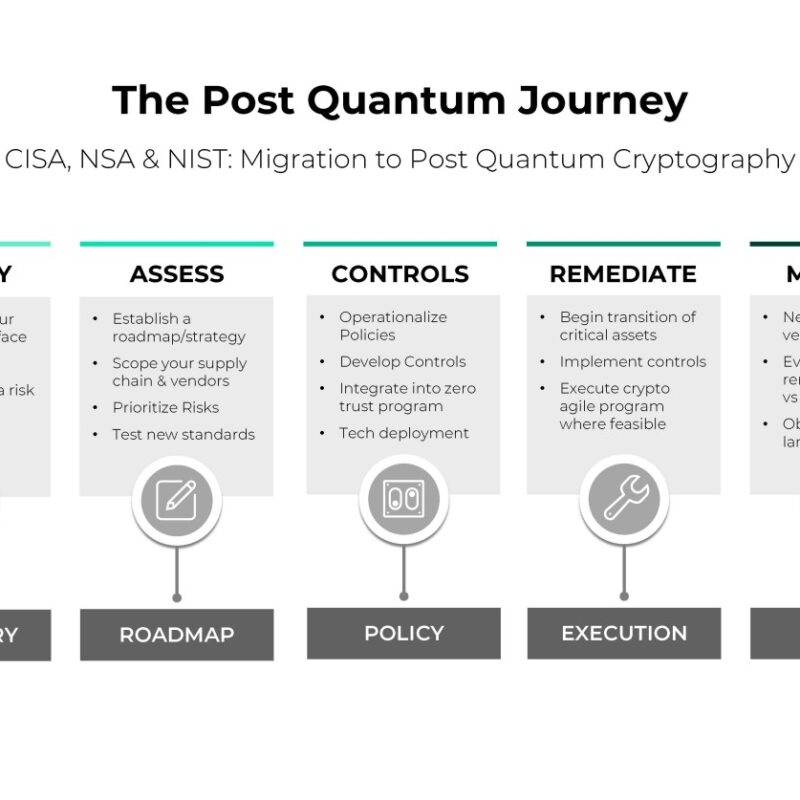
Understanding Cryptographic Inventory: A Cornerstone of Quantum-Ready Security
![The Post Quantum Journey CISA, NSA & NIST: Migration to Post Quantum Cryptography]()
Cryptographic discovery refers to the process of uncovering, analyzing, or creating new cryptographic algorithms, methods, or techniques to secure information.


